· business · 6 min read
Debunking the Myths: Is Zoom Really Safe for Business Meetings?
A clear-eyed look at Zoom’s security: what went wrong, what’s fixed, which risks remain, and an actionable checklist IT and meeting hosts can use right now to run secure business meetings.

Outcome first: Read this and you’ll know exactly when Zoom is safe for your organization, which concerns are real, and which settings stop the next embarrassing or risky incident. You’ll also get a short, practical checklist you can apply in the next five minutes.
Why this matters. Remote work is normal now. Sensitive meetings happen over video. If your conferencing tool isn’t configured for security, you don’t have a platform problem - you have a process problem.
Quick verdict
Short answer: Zoom can be safe for business meetings - but not automatically. It’s a capable, feature-rich platform with strong security controls when properly configured and managed. It had high-profile problems early on; many of those were fixed, and Zoom added more enterprise features (including optional end-to-end encryption). That said, no platform is inherently secure without the right policies, updates, and user training.
The simple context: what went wrong - and what changed
- In 2020 Zoom faced a wave of issues - “Zoombombing” incidents, some privacy and encryption misunderstandings, and rushed feature roll-outs that highlighted gaps.
- Zoom responded quickly - public roadmaps, security engineering hires, policy changes, and new features such as meeting controls and an optional end-to-end encryption (E2EE) mode. See Zoom’s Trust Center and E2EE announcement for details.
- National cybersecurity agencies published guidance for videoconferencing, urging organizations to choose secure defaults and apply policy. See the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the UK’s National Cyber Security Centre (NCSC) for practical guidance: CISA Telework Guidance · NCSC Video Conferencing Guidance.
Bottom line: the platform matured. The security conversation moved from “Is Zoom safe?” to “How do we use Zoom safely?”
Four common myths - debunked
Myth 1: “Zoom isn’t encrypted.”
Fact: Zoom uses strong encryption for meeting traffic (including AES-GCM). But encryption modes matter. Zoom offers transport-layer encryption by default (protects meeting traffic in transit) and an optional E2EE mode that provides additional guarantees - with tradeoffs (for example, some cloud features are unavailable when E2EE is enabled). See Zoom’s security whitepaper for specifics: Zoom Security White Paper.
Myth 2: “Only paid customers can use E2EE.”
Fact: Zoom’s E2EE option was designed to be available to both free and paid users, although enabling it changes feature availability (e.g., recordings to the cloud and some third-party integrations don’t work under E2EE). The choice is deliberate - a privacy vs. convenience tradeoff. Zoom E2EE announcement.
Myth 3: “Zoom is fundamentally insecure for business.”
Fact: No major conferencing vendor is immune to vulnerabilities, but Zoom provides enterprise-grade controls: account-level security policies, single sign-on (SSO), multi-factor authentication (MFA), role-based host controls, logging, encryption, and more. When these are used properly, they meet the needs of most businesses.
Myth 4: “If the vendor fixes things, we’re done.”
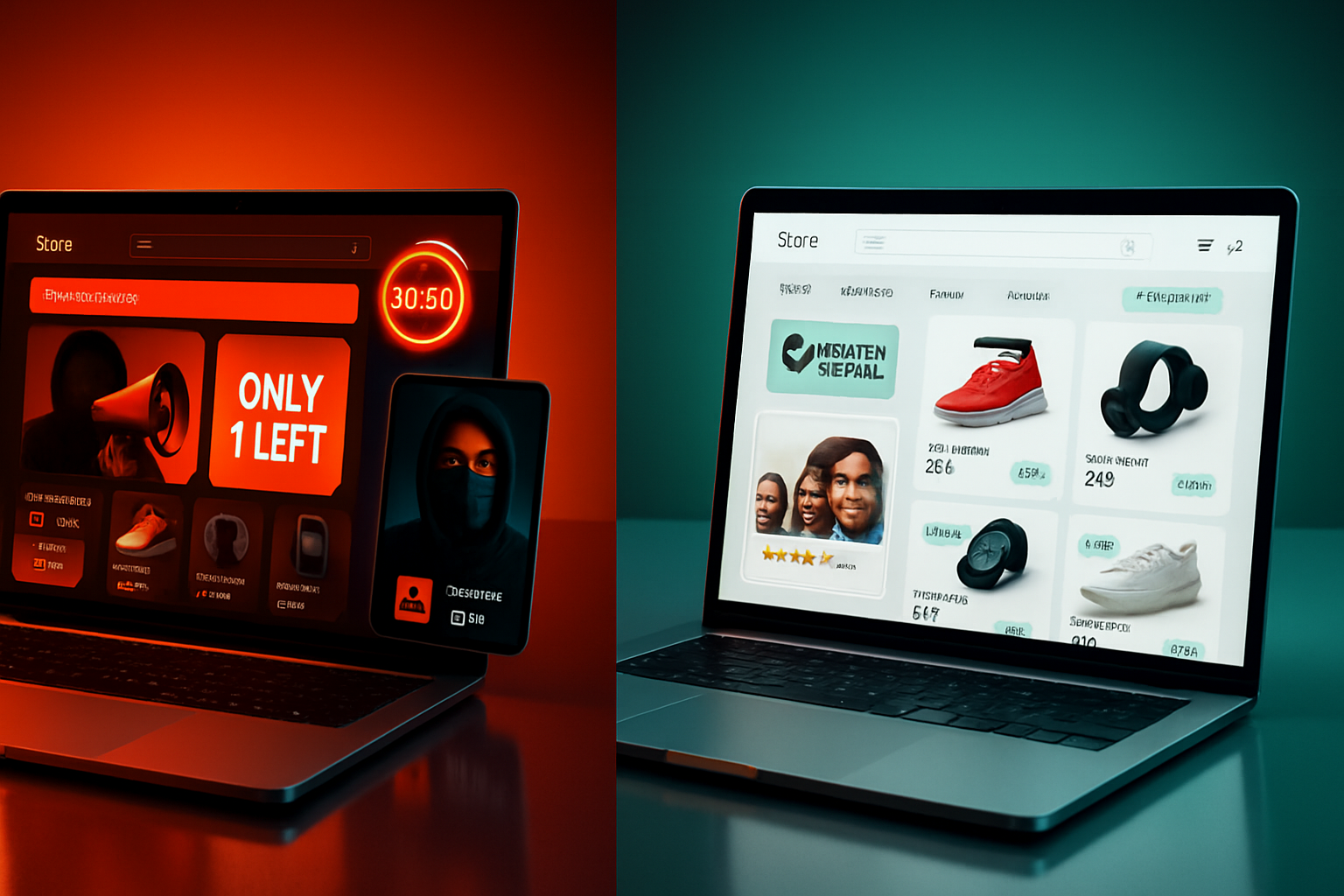
Fact: Platform hardening is necessary but not sufficient. Human error (sharing links publicly, not using authentication, misconfigured meetings) is the most common cause of incidents.
What ‘safe’ actually looks like - a practical checklist
Use this checklist for every business meeting. Many items can be enforced by IT centrally.
- Update clients - Require the latest Zoom client and browser updates. Attackers exploit outdated software.
- Use waiting rooms or meeting passcodes - If you can only enable one thing quickly, turn on the waiting room or require a passcode.
- Restrict screen sharing - Set screen-sharing to host-only by default. Enable participant sharing only when needed.
- Require authentication for sensitive meetings - Limit joins to users signed into your company SSO or approved domains.
- Lock the meeting after it starts - For high-sensitivity sessions, lock once all expected participants are present.
- Disable “Join before host” for official meetings - Prevent accidental starts and unmoderated sessions.
- Turn off file transfer and private chat if not needed - Reduce data leakage pathways.
- Don’t use Personal Meeting IDs (PMI) for public meetings - Generate unique meeting IDs for each session.
- Consider E2EE for high-sensitivity calls - Use it when confidentiality outweighs the convenience of cloud-recording and integrations.
- Enforce MFA and SSO at the account level - Prevent account takeover.
- Educate users - Teach staff how to share meeting links privately, recognize suspicious participants, and report incidents.
Apply these now. They’re fast to implement and stop most common issues.
Admin controls and policies IT teams should adopt
If you manage Zoom at the organizational level, these are the most impactful controls.
- Account and group-level policies - Configure secure defaults (waiting rooms, passcodes, restricted screen sharing) at the account or group level so users can’t accidentally expose meetings.
- SSO and SCIM provisioning - Use SSO for identity and SCIM for provisioning to keep user lists and access centralized.
- Enforce client version and device policies - Block legacy clients that lack security improvements.
- Audit and logging - Enable meeting reports, device logs, and audit trails. Integrate logs with your SIEM for detection and response.
- Record management - Restrict cloud recordings and apply access controls and encryption for stored recordings.
- App marketplace controls - Review and whitelist integrations. Disable third-party apps that aren’t vetted.
- Incident response plan - Add videoconference incidents to your IR playbook (revoking access tokens, rotating links, informing participants, and conducting a post-incident review).
When to use E2EE - and when not to
E2EE provides the strongest confidentiality guarantees because only participants hold the keys. Use it for highly sensitive discussions (executive meetings, legal strategy, M&A talks, patient consultations). But understand the tradeoffs:
- Some features (cloud recording, live transcription, third-party apps, dial-in for PSTN) may be disabled with E2EE.
- E2EE can complicate enterprise monitoring and compliance workflows.
- Key management choices affect trust - Zoom’s E2EE can use Zoom’s key servers or client-generated keys depending on configuration.
If your organization depends on cloud recording, transcription, or eDiscovery workflows, weigh whether those operational needs outweigh the confidentiality benefits of E2EE.
Alternatives - should you switch platforms?
Every major vendor has tradeoffs. Microsoft Teams, Google Meet, Webex, and others each offer different enterprise controls, compliance options, and integrations. Choose by risk model:
- If tight integration with an existing identity/compliance stack matters, choose the vendor that best fits your ecosystem (e.g., Teams for Microsoft-centric shops).
- If absolute confidentiality (and minimal vendor access to content) is the top priority, evaluate E2EE support and the operational limits it imposes.
- If you lack confidence managing conferencing at scale, consider a vendor with mature admin tooling and professional services.
Switching platforms can be disruptive. A better first step is usually to harden your existing deployment and test policies against realistic scenarios.
A pragmatic decision framework (5 minutes)
- Classify meeting sensitivity - low (all-hands), medium (client demos), high (legal, IP, HR).
- Apply baseline controls for all meetings - updated clients, waiting room or passcode, restricted sharing.
- For high-sensitivity - require authenticated users, lock meeting, enable E2EE if acceptable operationally.
- Monitor - collect logs and review usage monthly.
- Train - run a 10-minute session for meeting owners on secure meeting setup.
Do this and you’ll eliminate most risks without overcomplicating workflows.
Final thoughts
Zoom was a target in 2020 - and it responded. The platform now provides strong cryptography, enterprise controls, and an optional E2EE mode. But security isn’t a checkbox you hand to a vendor. It’s a combination of product features, account-level configuration, and human behavior. Configure the defaults. Limit who can join. Train your people. Monitor and respond.
You don’t have to fear Zoom. You do have to treat it like a business system: secure by configuration, enforced by policy, and backed by training and monitoring. When you do that, Zoom becomes a reliable tool - not a liability.
References
- Zoom Trust Center: https://explore.zoom.us/en/trust/
- Zoom introduces end-to-end encryption: https://blog.zoom.us/zoom-introduces-end-to-end-encryption/
- Zoom Security White Paper: https://explore.zoom.us/docs/doc/Zoom-Security-White-Paper.pdf
- CISA – Telework Security Guidance: https://www.cisa.gov/telework-security
- NCSC – Video Conferencing Security Guidance: https://www.ncsc.gov.uk/guidance/video-conferencing-services-security-guidance-organisations